This is a short list of the features and technologies behind Firejail:
Linux namespaces
The core technology is Linux Namespaces, a lightweight form of virtualization. Basically, the app gets its own filesystem, network stack, and kernel interface.
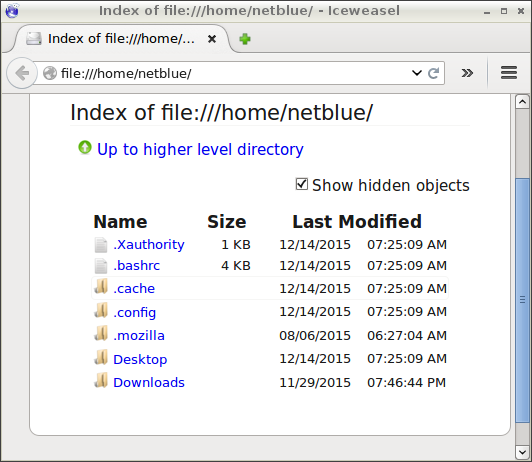
Access Control
On top of the regular file system, we deploy a very efficient Mandatory Access Control. It restricts application access to the underlying file system on a file by file basis.
Security filters
The following security filters are currently implemented:
- seccomp-bpf – reduce the attack surface of the kernel by attaching a system call filter to the processes running inside the sandbox.
- communication protocol filter – most default profiles allow only UNIX, IPv4 and IPv6 communication protocols.
- noroot user namespace – install a user namespace with only one valid user, the current user.
- Linux capabilities – a set of distinct root privileges that can be independently enabled or disabled (POSIX 1003.1e).
- X11 sandboxing support is built around two external X11 server software packages, Xpra and Xephyr.
- D-BUS filtering
- AppArmor and SELinux support if available on the host system.

Networking

Firejail can attach a new, isolated TCP/IP stack to the sandbox. The new stack comes with its own routing table, firewall, and set of interfaces. We support classic firewall filter configurations based on iptables, and dynamic firewall filters (see –netlock).
Firejail inspects the network traffic (see –nettrace), and allows the user to analyze and monitor application behavior.


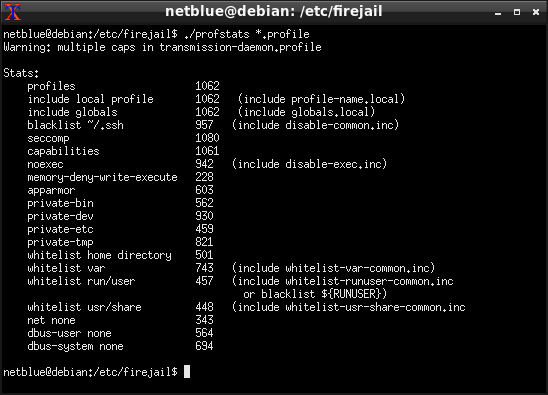
Security profiles
Located in /etc/firejail directory, profile files describe the filesystem container, the security filters and network configuration for each application supported by default by Firejail. Currently, more than 1000 different applications are supported,
Universal packaging formats
Firejail supports AppImage packaging format natively. Simply add –appimage command line option and the package is mounted and run inside the sandbox.
Statistics and monitoring
Firejail provides a large number of options to track all the aspects of sandboxed applications. This includes monitoring CPU/memory/bandwidth usage, tracing system calls, monitoring exec and fork events, and logging accesses to blacklisted files and directories.

We also have available a simple auditing tool, jailcheck. Running as root, the program attaches itself to all running sandboxes, and looks for possible security problems with user configuration.

Graphical user interface
A GUI application, Firetools, is available as a separate software package.



Pingback: Обновление системы изоляции приложений Firejail 0.9.42 | Linux-House.ru
Hi there,
Sorry if this is not the smartest to ask and ive overlooked in my complacency.
Firejail is amazing, thank you. Ease of use and abilities. Hats off to you, though had me thinking. Can it box the entire OS and have more box’s inside that as they usually are set on chrome and firefox etc etc..?
I’m a week into my journey of Linux, apologies again if this is a bit of a….idioitic question
LikeLike
Thanks for your kind words. The idea so far was to target specific applications, such as Firefox and Chromium, or closed source apps like Steam and Skype. We are moving in the direction of sandboxing a full OS, but it will take some time to get there.
LikeLike
Pingback: Firejail Tutorial – eirenicon llc
There’s a typo in the HTML for this page: https://firejail.wordpress.com/features-3/
Line 230 should read:
Resource allocation
Not:
Resource allocation
Thanks for the cool product!
LikeLike
Sorry, it appears I can’t edit my previous post.
The edit in line 230 should be from “#resurces” to “#resources”.
LikeLike
I guess I’ve missed this one! Thanks!
LikeLike
Pingback: Firejail - Securely Run Untrusted Applications in Linux
Pingback: Securely Run Untrusted Applications in Linux | Top Tech Stories
Pingback: Securely Run Untrusted Applications in Linux | Tech News One
Pingback: Firejail – Securely Run Untrusted Applications in Linux – Clockwork Network
Pingback: Firejail, ejecuta de forma segura aplicaciones no confiables en Ubuntu
Pingback: Выпуск системы изоляции приложений Firejail 0.9.60 — AllUNIX.ru — Всероссийский портал о UNIX-системах
Pingback: Выпуск системы изоляции приложений Firejail 0.9.60 |
Pingback: Выпуск системы изоляции приложений Firejail 0.9.62 |
Pingback: Firejail - Führen Sie nicht vertrauenswürdige Anwendungen unter Linux sicher aus - okidk.de
Pingback: Firejail - безопасный запуск потенциально уязвимых приложений
Pingback: [linux] 파일 열기, 분기 등을 방지하는 Linux의 샌드 박스에서 신뢰할 수없는 C 프로그램을 실행 하시겠습니까? - 리뷰나라
Pingback: Execute com segurança aplicativos não confiáveis no Linux - Okdk
Pingback: Firejail - Chạy an toàn các ứng dụng không đáng tin cậy trong Linux - 2Error.net
Pingback: ¿Ejecutar un programa C que no es de confianza en un espacio aislado en Linux que le impide abrir archivos, bifurcarse, etc.? - Fallosweb.com
Pingback: Firejail – Securely Run Untrusted Applications in Linux - CyberZ.in